The implementation of mobile communications standards such as 5G and, in the future, 6G in private campus networks offers great potential for improving medical care by networking medical resources and enabling the rapid exchange of even large amounts of information. However, the demands on data security and the resilience of IT systems are enormous, especially in the medical field.
As part of the medCS.5 research project, we have developed prototype solutions that will help solve these problems in the future. How can a campus network be secured against such threats?
The two-step approach for maximum 5G resilience
A cyberattack in a hospital can have devastating consequences. To counter this high potential for damage, a mere reaction is not enough. Our solution therefore pursues a two-stage strategy:
1. Prevention: The network is hardened against attacks through simulations before it is put into operation.
2. Detection: The network must be able to respond dynamically to threats during operation.
Both stages are implemented through a combination of network simulation and the use of AI-supported analysis tools.
In order to identify types of threats in advance and in a protected environment, it is possible to simulate communication within a 5G network. This involves simulating communication processes at the application level. This allows both inconspicuous and suspicious behavior within the network to be replicated, indicating potential threats.
The starting point for the simulation is the patient journey through the hospital. At the various stages of their journey, patients and, subsequently, their data come into contact with the hospital’s IT infrastructure, for example during admission or during the individual treatment phases. The medical devices and IT end devices involved each form a node within the campus network. Each network node is exposed to potential dangers from cyberattacks. The individual steps of the patient journey can therefore be assigned locations, involved actors, hardware components, signal and data types, and cybersecurity risks. The relevant threat scenarios range from phishing, man-in-the-middle and malware attacks to data manipulation and theft to ransomware and edge cloud attacks.
With the help of the mappings provided by the mapping process, suitable test sequences can then be derived as part of a network simulation. A simulation and test environment was developed specifically for this purpose.
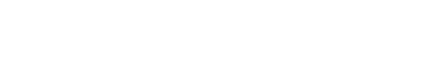
The 5G campus network of the Fraunhofer Heinrich Hertz Institute in Berlin was used to carry out the simulation. The hardware environment consisted of several computers and virtual machines (hosts) connected to the 5G network. The simulation was controlled centrally from one of the hosts.
Each host can simulate several medical devices and applications simultaneously. Implementation is carried out using Python scripts. These are executed in a virtualized environment in their own Docker container. Containers encapsulate the simulation code to be executed and all components required for execution, e.g., library functions and operating system services, in a portable and highly scalable instance. This means that the implemented simulations can be executed independently on each host and can be distributed between them as desired (see Figure 1).
The automated behavior of individual simulations is controlled by the simulations themselves. Markov automata were used to generate more realistic behavior patterns. Markov automata are state transition systems whose transitions are activated according to predefined probabilities.
For a better understanding, Figure 2 shows a greatly simplified Markov automaton whose states represent the actions that can be triggered by the user of a patient database when accessing it as part of an examination. The weighted edges between the states indicate the probability of a follow-up action. In this example, it is assumed that an examined patient has a 50% probability of being an existing patient. During the course of treatment, the patient file is opened (Read Patient) and updated after the examination (Update Patient). However, if the patient is a new patient, a new patient file is created (Create Patient) and also updated after the examination. The automat then returns to its initial state.
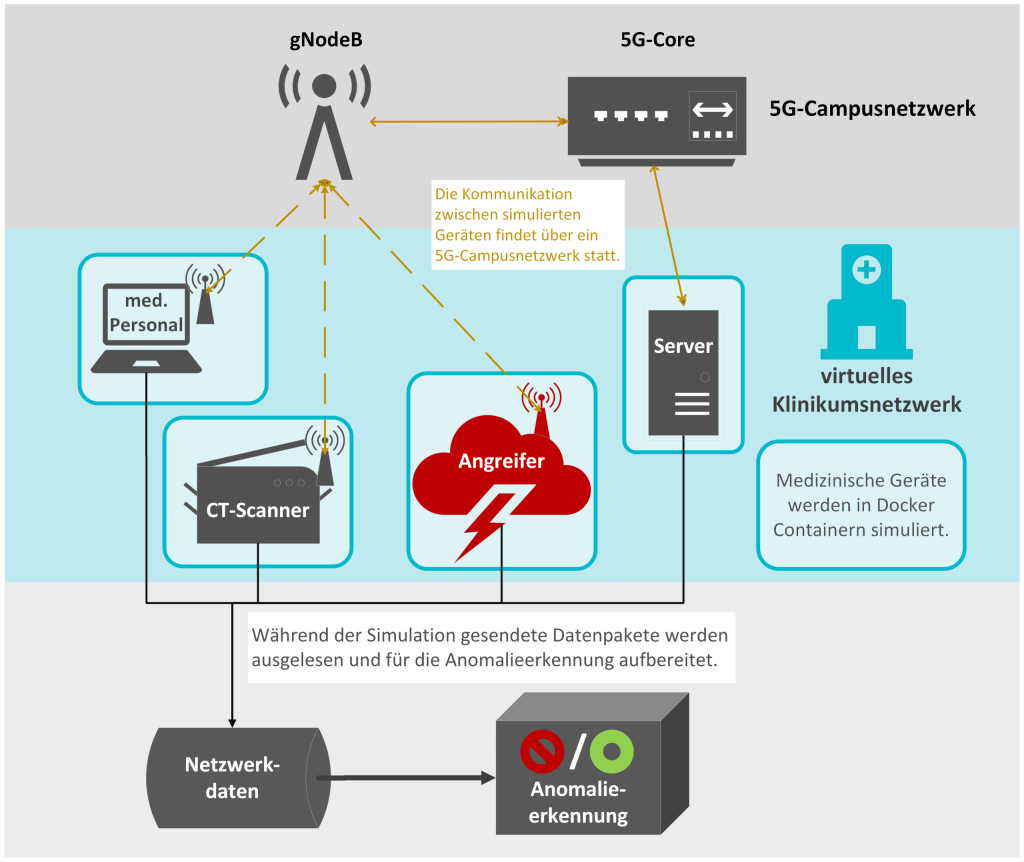
Simulated devices can be replicated to create larger campus networks. Due to the probabilistic state transitions of the Markov automata controlling the simulation, the behavior of replicated devices and applications is not identical but varies in its specific form.
In the security test, the content of the data transferred via the communication network is of little importance. Therefore, to simulate data transfer, data in typical formats from the clinical environment is randomly generated and transmitted for each action generated by the Markov automata. For example, in imaging procedures, image series in DICOM format (Digital Imaging and Communications in Medicine) are generated with randomly selected pixel values and metadata.
Patient data (personal data and examination findings) are generated in FHIR format (Fast Health Interoperability Resources). For this purpose, sample data are used as a basis and the individual fields of the data record are randomly varied
Various types of attacks are used to simulate abnormal data traffic. One example is hijacking, in which cybercriminals take control of a device in order to access patent data, for example. The behavior patterns resulting from this attack can be achieved by reconfiguring the Markov automata: While in normal operation only a single patient file is processed at a time, an attacker might be interested in reading as much data as possible in the shortest possible time. Accordingly, only the “ReadPatient” action would be executed without any waiting time between actions.
The data obtained in the simulation can then be used to train an AI-based anomaly detection system that enables live monitoring of the real campus network to detect potential threats. The simulation data is processed according to specific criteria and tagged with metadata. It is then classified and grouped into larger blocks with similar characteristics. The AI component of the anomaly detection system is trained on the basis of network behavior classified as normal. Deviations from this are therefore classified as anomalies.
Anomaly detection is based on a two-step process. In the first step, data from various devices and applications that have been recorded at overlapping times is entered into a machine learning model that has been trained with normal behavior data and can distinguish between the different data streams. If a data stream is not recognized by this system, it is forwarded in the second step to another ML model (autoencoder) that has been trained to imitate normal data streams through encoding (reduction of the data dimension) and subsequent decoding (reconstruction of the original data dimension). Based on the accuracy of the imitation (difference between the input and output data streams of the autoencoder), it can then be determined whether the incoming data stream represents typical or abnormal behavior.
To ensure the performance of the detection system, it is implemented as a hardware-accelerated solution on an FPGA.
The secure processing of sensitive data is the biggest hurdle for 5G in medicine. Our results show that combining simulation techniques and machine learning can be used to develop solutions that significantly increase the 5G resilience of campus networks. Continuous analysis also enables operators to respond proactively to changing threat situations. To this end, we have developed a service portfolio that allows us to provide you with optimal support.

I am your sales representative and will be happy to advise you on all questions relating to our services and products! Get in touch or simply make an appointment for a free consultation call.
Sebastian Stritz
E-Mail: sebastian.stritz@itpower.de
Phone: +49 (0)30 6098501-17
